Build a Dataspace for your needs
Our IOXIO Dataspace™ SaaS solution is intended for customizability for different use-cases, and we can assist you with building the Dataspace for your specific needs. Every Dataspace can define its own Data Products, trust layers, policies, and what industry is in their focus.
We specialize in helping people identify the relevant data, parties, and operating processes and our world class experts will help you build an ecosystem around your data needs. We are already working on multiple initiatives, so we'd also like to try and connect you with the existing Dataspaces and find an easy way for you to participate in the future of data.
For Dataspaces that are not yet ready for production we also provide a demo-grade Login Portal and Consent Portal, to minimize the steps necessary to try out how data sharing can work. Additionally, our Sandbox environment provides your developers a free and safe place to try the technology before spending the effort on creating your own Dataspace.
Contact us if you want to learn more about building Dataspaces or how to join one!
Customizable dataspace architecture
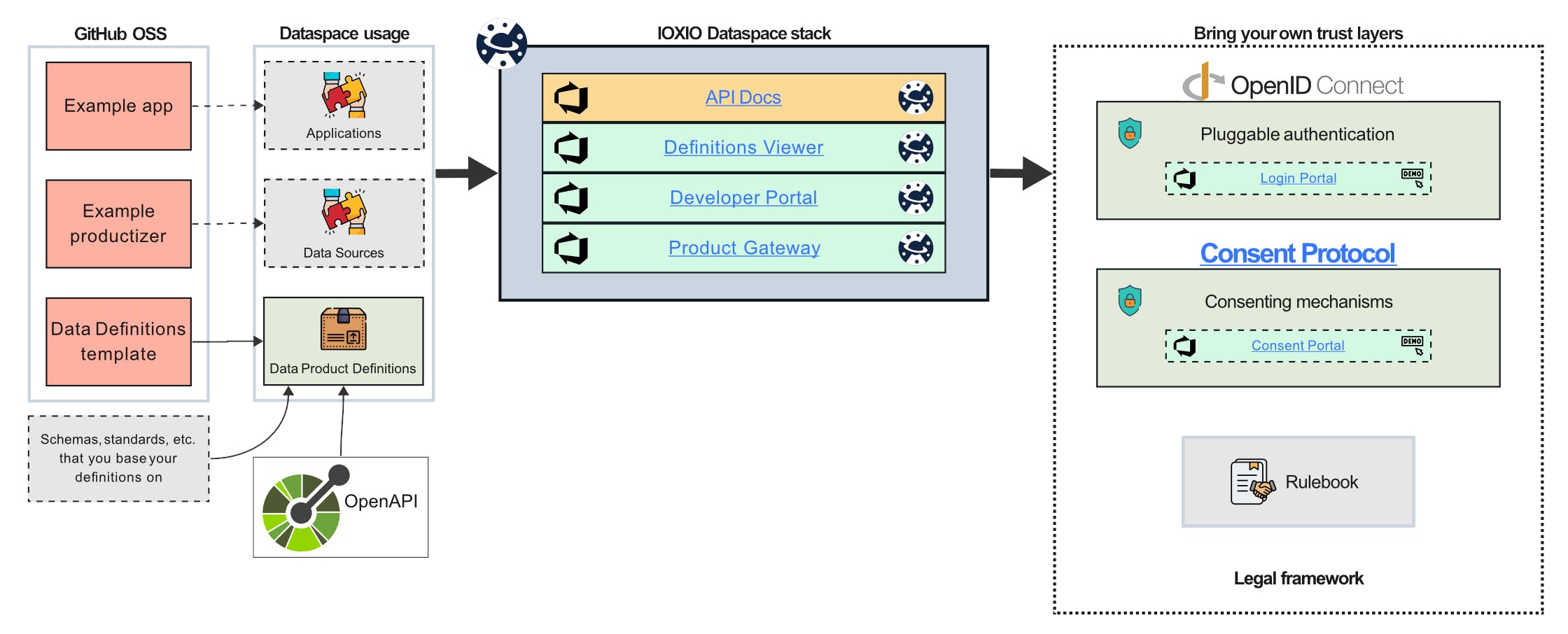
Every dataspace built on the IOXIO Dataspace™ architecture is slightly different, but based on strict standards. The core pluggable elements of a Dataspace are trust layers, and data definitions. For trust layers we support an OpenID Connect based authentication provider, Open Consent Protocol based consent providers, and the legal framework is provided via Rulebooks. For the data definitions we use a subset of OpenAPI 3.0 to standardize HTTP JSON APIs, and they are published on a public GitHub repository for everyone to see and participate on the definition work.
The data definitions chosen for the Dataspace define the available Data Products that can be shared on the Dataspace, standardizing the communication methods and data payloads that can be used. This allows us to finally productize data, and make it possible for multiple data vendors to compete on a fair market and application vendors to choose whose data they feel is best suited for their needs, with minimal changes necessary when they change providers.
Built on the internet best practices

The trust mechanisms on the IOXIO Dataspace™ architecture are built on a decentralized model based on internet best practices currently in widespread use. There's no hocus pocus, no new cryptography invented, you only need to use open standards and architecture mixed with industry standards with comprehensive ecosystems of implementations and tools.
All the parties host their own public keys using JSON Web Key Sets, which then are used for verifying tokens and messages, as well as encryption, whenever it is needed. Trust in JWKS is brought by the existing mechanisms on the internet, DNSSEC, SSL certificates (incl. Extended Validation), and so on.
JSON Web Tokens, IETF HTTP Message Signatures and JSON Web Signatures, as well as JSON Web Encryption provide a solid set of tools for providing trust on multiple layers, including verifying authentication or consent tokens, to ensuring data hasn't been tampered with, or confidentiality.
You can also read more about our trust architecture.
Standardized data makes products

When we agree on standard sizes of toast and toasters, selling a competing toaster becomes a lot easier. Similarly we believe that standardizing data products and the ways of transferring them will make it possible to get data moving, and when multiple vendors are providing their own data in standard formats we will empower a new modern data economy, unleashing new kinds of practical applications.
The data vendors and application developers alike can collaborate in the work for defining data products on the Dataspace in the Definitions repository, and the results are published on the Dataspace so everyone can easily follow the agreed standards. You will find the currently available Data Product definitions on the Definitions Viewer, and technical details in the API Docs.
Explore our data definition guide or the Youtube video tutorial for productizing data.
Great tools for application developers

Application developers on the IOXIO Dataspaces get many tools at their disposal, ranging from easy tools to find and analyze the available Data Products, to technical API documentation, as well as example code.
The application integration can be simplified to just a couple of steps. You start off by finding the data sources you want to use on the dataspace on the Developer Portal, you can then check the Definitions Viewer and API Docs for details on how to use them. If the data product requires authentication, you will need to register your application and integrate to the OpenID Connect -login flow. Lastly, you just need to follow the Data Product definition and request the data product from your selected source, the Developer Portal will tell you the API endpoint.
The IOXIO Dataspace™ architecture does not force any specific technology choices, deployment models, etc. onto application developers. You know how your applications should be built, and we step out of your way and provide the capabilities to easily bring data into them.
Explore our application developer guides and open source example application for more information.
Bringing data available is a breeze

Making your data available has never been easier. Data vendors can participate in the common work to define the data models with other data vendors and application developers, or they can choose to just use the existing Data Definitions and bring their valuable data to others.
The data source integration can be simplified to just a couple of steps. You start off by finding the data definition you want to provide data on the dataspace in the Definitions Viewer, you can then check API Docs and the OpenAPI Specs for details on how to use them. If the data product requires authentication, you will need verify the authentication tokens in your data source. Once your productizer is complete, you register it on the Developer Portal, test it, and publish it.
The IOXIO Dataspace™ architecture does not force any specific technology choices, deployment models, etc. onto data vendors. You know best how to build your HTTP JSON APIs according to the data product spec, and we don't want to step on your toes.
Explore our data integrator guides and open source example productizer for more information.
Personal data access consenting

We firmly believe that people should be in control of their own data, and what it is used for. We've worked a long time with many experts to develop the concept of an Open Consent Protocol, capable of providing users real control over who uses their data and for what. No more vague "accept all terms and conditions", but strict control over who can use your data, from what source, and for what purposes.
We have documented the Open Consent Protocol, tested it with multiple parties, and built a demo-grade Consent Portal to demonstrate the capabilities. You can try out our My Company demo application.
Documentation and integration guides for applications and data sources are of course easily available for your developers.
Current focus and limits
We're currently heavily focusing on the most impactful solutions. In practice our focus is on API -based data transfer, simple JSON POST requests and JSON responses. We have future plans for expanding to e.g. streams, WebSub, and various ways to use our technology for the "handshake" but doing the bulk transfer directly between parties - e.g. for large file transfers. These are however future plans, so we are not yet in a stage we would call ready for "General Purpose" use.
We are currently building capabilities for production readiness, meaning you shouldn't expect to be able to bring your most sensitive data onboard immediately, but we will happily assist you in trying out the technology with safe demo data, and take your feedback for requirements for going to production with your case.
Configuration and documentation

Our Dataspaces are built on the assumption that there will be multiple dataspaces, and we want to make it as easy as possible for you to start using a dataspace. There's little need for hard-coded magic, as we provide many public configuration files for the services, starting from our Dataspace configuration file which tells your applications how to talk to the Dataspace and where to discover the various services in it.
All the parties on the Dataspace, including us, the application developers, and data vendors, publish their own Party configuration file, which documents things like where their public keys can be found. As any OpenID Connect authentication provider publishes an OpenID Connect configuration file, our Consent Portal provides a similar Consent Configuration file. Finally, the data you share on our Dataspaces is configured via the Data Product Definitions.
All of the information you need is easily available on our Developer Portal, but if you ever have issues or questions, our IOXIO® Community Slack is there for you.
Trying out our Dataspace technology
Don't just take our word for it, we are proud to have you try it all out for free with zero strings attached. The two main environments you can test our Dataspace technology are our Sandbox and the Virtual Finland Testbed environment.
If you are interested in an overview of the capabilities, our Showroom and My Company demo application are the perfect places to get started. We also have made a number of Youtube videos explaining the concepts as well as the pilots we've built so far, and you can read more about this on the Cases section.
If you have any further questions, we're always available for a chat so don't hesitate to contact us!